New security breaches are occurring on an almost daily basis. Attackers often gather breach data in search of attacking valid user accounts on other websites, such as the 773 million unique addresses found in the “collection #1 data breach”. A normal user might use the same email address or login on multiple websites. An attacker is motivated to understand to fingerprint a user’s presence on the Internet and gain access to their account, credit cards, personal data, or their shopping history.
Methods Of Determining Valid Users
To first determine if a user account is valid, attackers take advantage of a vulnerability called Valid Account Determination. Web application error messages on valid and invalid accounts can notify the attacker to which user accounts are registered in the system. Check the following six common methods of valid account determination in your application!
Before starting, make sure that you know of one valid and invalid user account within the application. It makes it easier to decipher and compare the error messages you encounter.
Error Messages On Main Login Screen
Entering an invalid username and password on the login screen might provide an error message saying the user account does not exist.
Entering a valid username, but a bad password might show the user account is valid – but a bad password has been entered.
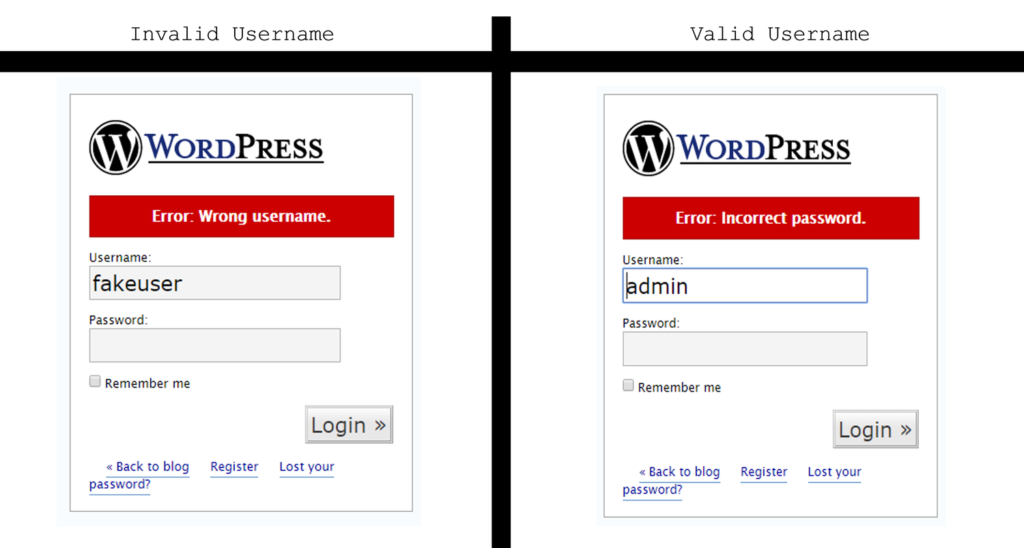
To fix this issue, ensure that all error messages are the same, such as “The username and/or password are incorrect.”
Error Messages On Forgot My Username/Password Screen
Invalid usernames / email addresses may give you a “Sorry, this user account does not exist” error message. You should also look for messages such as “There was an error in finding your account.”
Valid user accounts will provide a success message in the response.
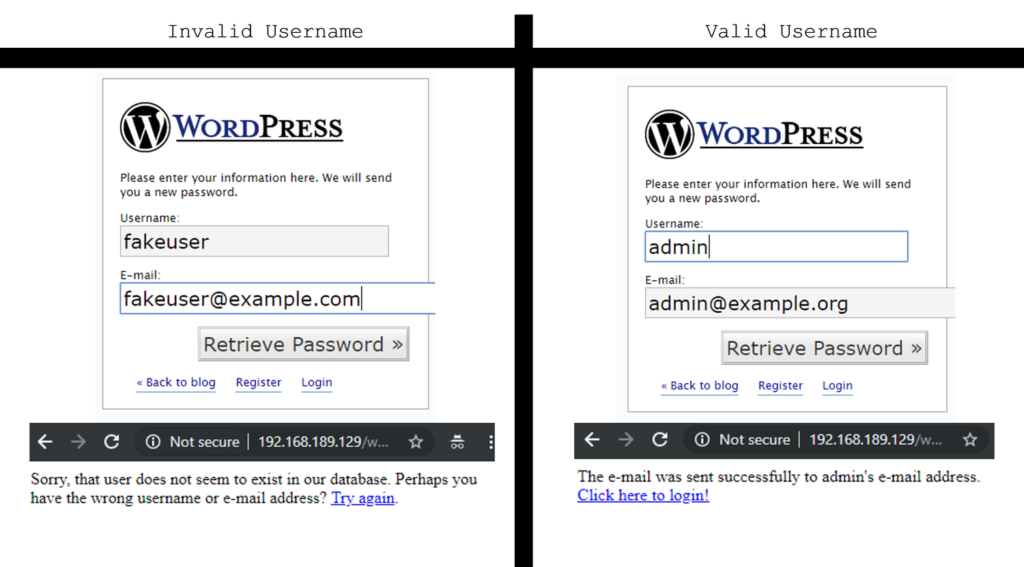
To resolve this issue, ensure that all error messages are the same. “If your username is valid, please check your email address for further instructions.”
Account Lockout
Attempt to lockout a valid account. After a successful lockout, attempt to lockout an invalid account. Once completed, retry logging into the valid user account. If you get an error message saying that valid account is locked, but you cannot ‘lock out’ an invalid account, you have successfully determined a valid user account.
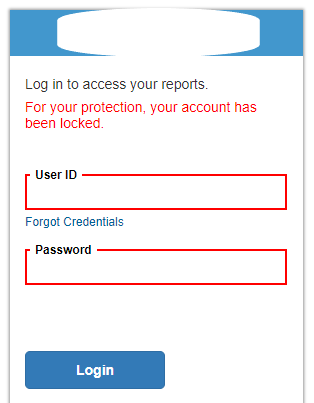
Apply the same logic and error messages on account lockouts to all users, even if that user may not exist within the application. To keep it simple, you can add a “An excessive number of attempts will lockout your user account” to the regular “Username/password is invalid” error message.
Attempt To Create An Account With A Known Email Address/User Account
Attempt to register a user with an already created username or email address. If it exists, you may see an error message saying the account already exists.
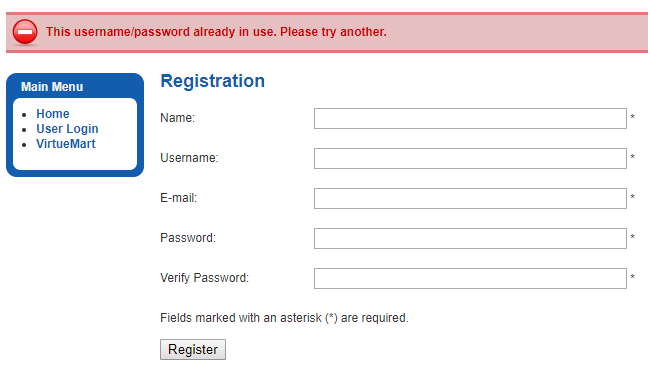
If possible, use an out-of-band user registration process to resolve this issue. When the user submits a username, provide a standard message stating “Please check your email to verify your user account.”
Email Unsubscribe Links
Unsubscribe functionality is often available without authentication. Attempting to unsubscribe an invalid account will usually get an error message.
Unsubscribing a valid account will often provide a success message.
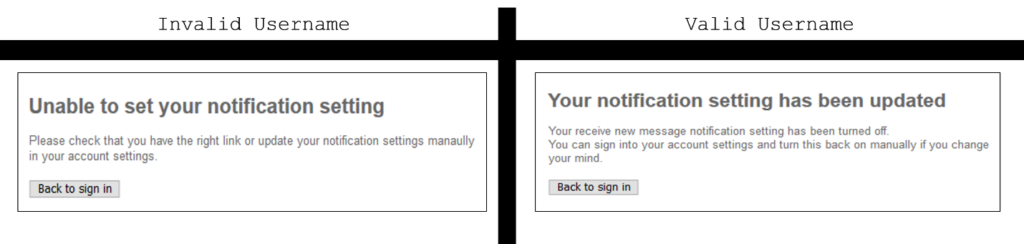
To resolve this issue, ensure that all error messages are the same, such as “Your unsubscribe request will be processed within 24 hours.”
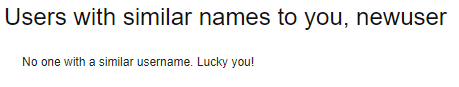
Maybe they intentionally built it into the app…
Username Similarity Built-In
Sometimes you get lucky and the application intentionally exposes other user accounts within the application or provides functionality to check usernames. Check out all user provided functionality and see what you can find.
For more information on how White Oak Security can help with web application security, please reach out via our contact page or take a look through the rest of our services page. Thank you for reading!
MORE FROM WHITE OAK SECURITY
White Oak Security is a highly skilled and knowledgeable cyber security and penetration testing company that works hard to get into the minds of opponents to help protect those we serve from malicious threats through expertise, integrity, and passion.
