I was recently combing through GitHub for a tool that I tend to use on mobile application penetration tests when I came across APKLeaks. I currently make use of Mobile Security Framework for discovering sensitive information within the APK files, but thought – why not try a new tool? ApkLeaks specifically scans APK files for URIs, endpoints, and secrets.
Check out this accompanying video to this blog, APKLeaks Pentesting Video, for more information.
APKLeaks Installation
There are a few ways to complete the installation:
- PyPi
- pip3 install apkleaks
- Source
- git clone https://github.com/dwisiswant0/apkleakscd apkleaks/
- pip3 install -r requirments.txt
- Docker
- docker pull dwisiswant0/apkleaks:latest
I chose to do Step 1 with PyPi – a simple installation and it worked perfectly on the new Mac M1.
APKLeaks Usage
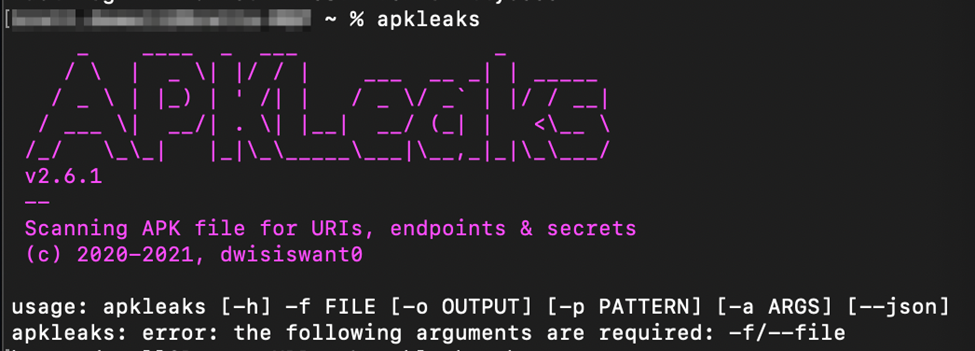
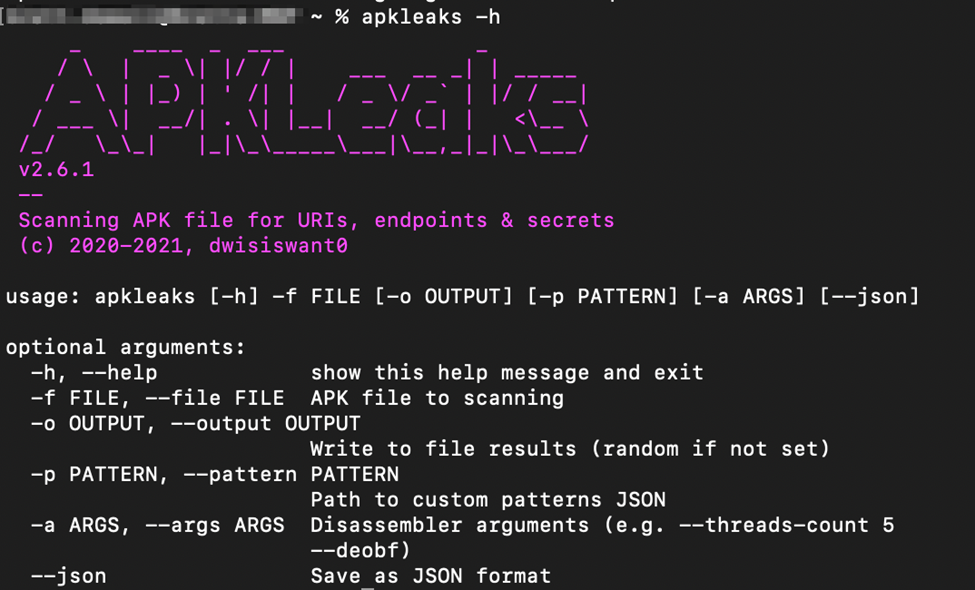
Running apkleaks from the terminal will bring up the basic help menu otherwise apkleaks -h will provide additional information on each of the flags allowed for execution.
Now let’s move into some real examples – I went ahead and downloaded a couple of APK files from APKPure to test this tool against. To prevent any exposure of the application tested against – I also blurred the output of the tool, but you get the jist of it.
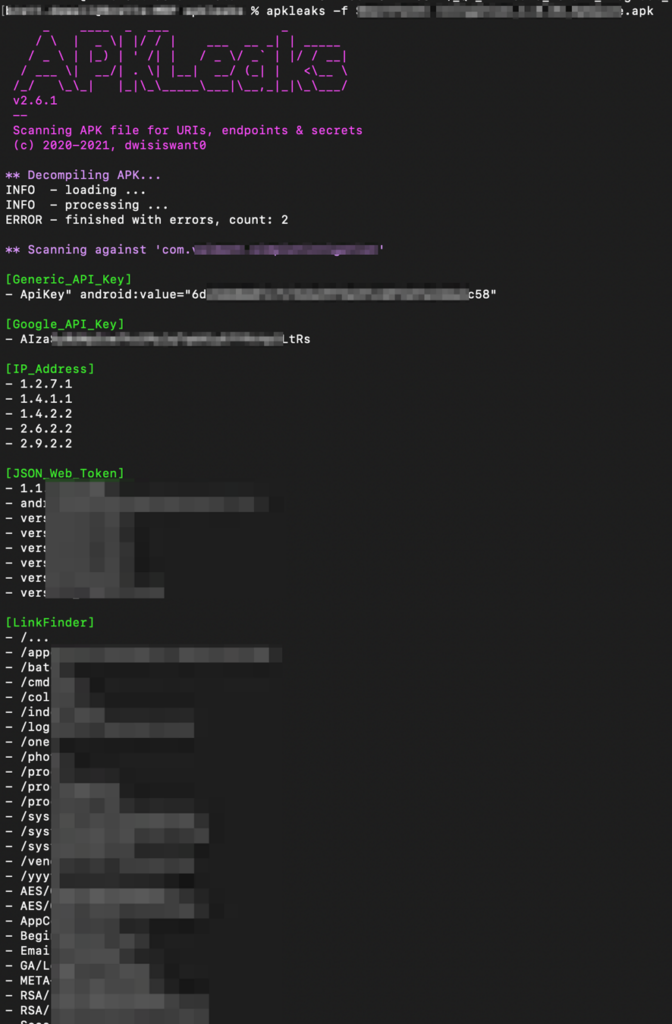
The above screenshot breaks down multiple categories the tool may discover items within the source code. I have noticed that quite a few of the items flagged have been false positives, however, the tool has a very high processing time that can provide additional items to review – it just makes sense to add this to my testing playbook when testing mobile applications.
MORE FROM WHITE OAK SECURITY
White Oak Security provides deep-dive offensive security testing. We are a highly skilled and knowledgeable cyber security and penetration testing company that works hard to help organizations strengthen their security posture by getting into the minds of opponents to try to protect those we serve from malicious threats through expertise, integrity, and passion.
Our unique industry experience allows us to offer a wide range of services to help analyze and test information security controls and provide guidance to prioritize and remediate vulnerabilities.
