On a recent Internal Penetration Test engagement, I was reviewing some Nessus scan data and came across an “Microsoft Windows SMB Shares Unprivileged Access” finding. As we can see from the screenshot below Nessus discovered an open Server Message Block (SMB) file share.
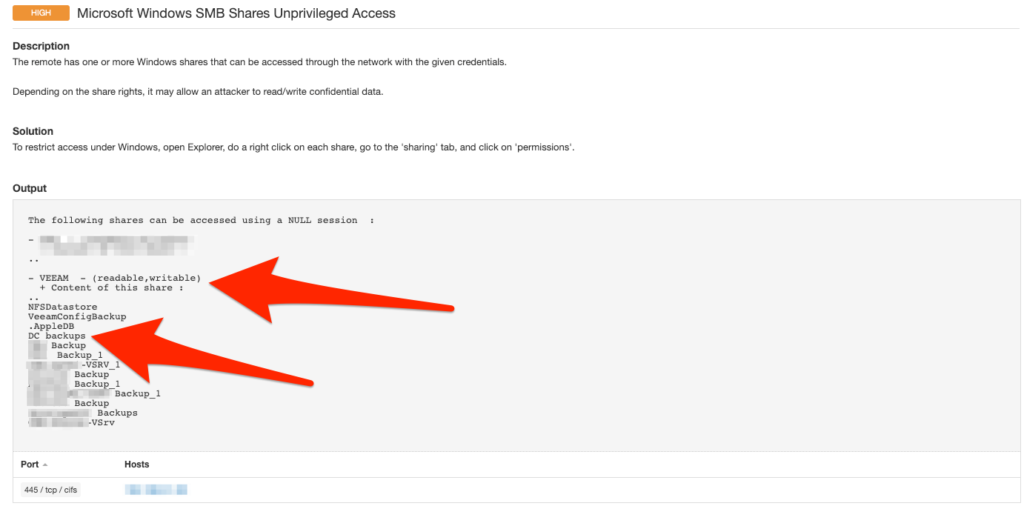
The folder discovered was labeled “VEEAM”. After navigating to the folder in question there were multiple sub-folders containing the following naming scheme (<hostname> backups). Making a quick Google search I discovered that VEEAM has multiple products and solutions, but in this instance it appears that the client is utilizing the Backup & Replication product. One very interesting sub-folder was the “DC Backups”.
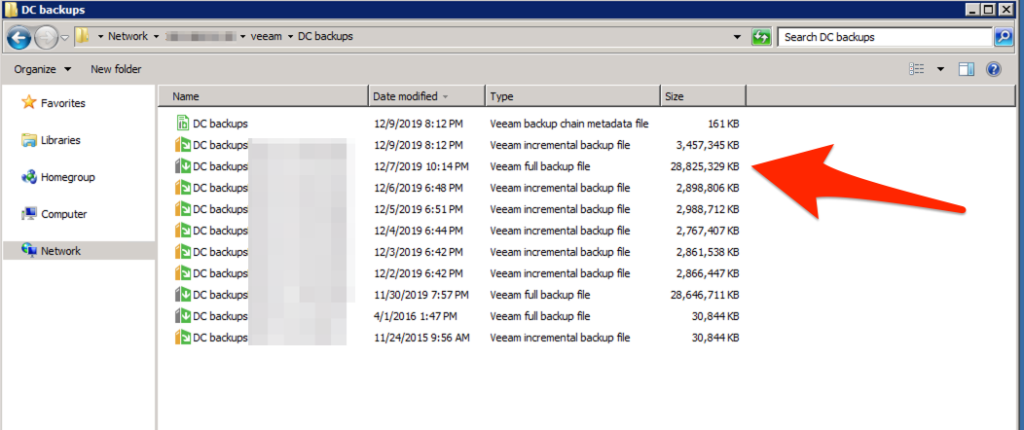
As an attacker, having access to a domain controller’s backups could result in total domain compromise. To begin manipulating the VEEAM backup file I started off by downloading the free version of VEEAM backup and replication software.
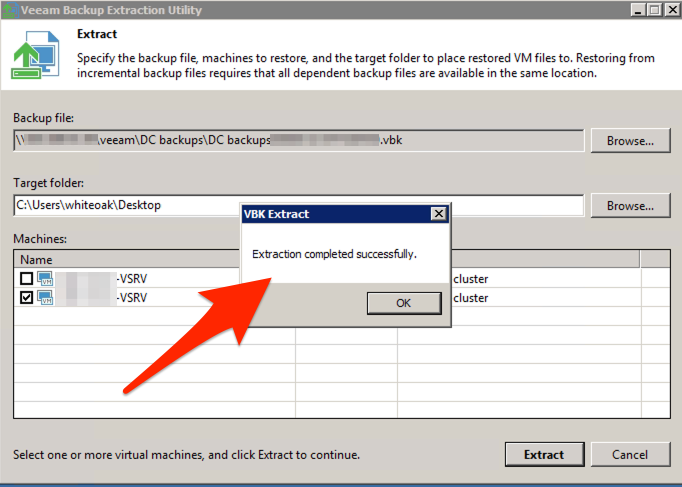
The installed Veeam software included a tool called “VBK Extract”, which allows for you to extract VBK files. Utilizing this tool we can begin the extraction process.
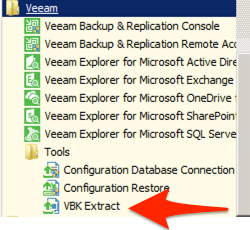
With the extraction utility opened, the process is pretty straight forward. Select the backup file, select a target extraction folder, and select a virtual machine backup.

When the extraction process completes the user will receive a pop-up alert confirming the extraction has completed successfully.
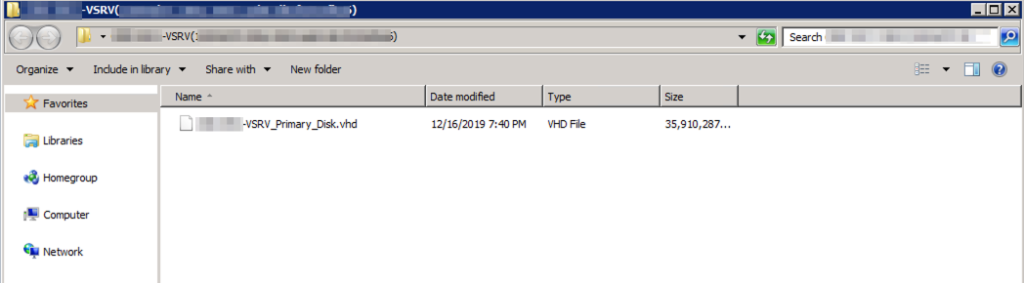
The extraction tool converted the VBK file to a Virtual Hard Disk (VHD) format.
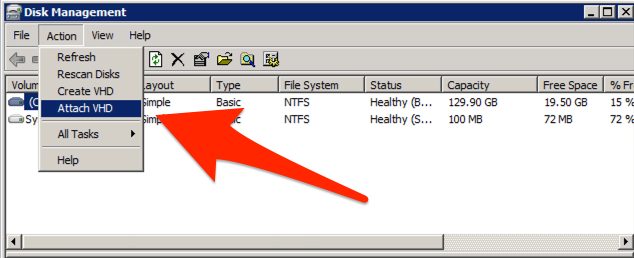
This format can be mounted natively within Windows utilizing Disk Management. As we see below Disk Management allows for the action “Attach VHD”.
With the VHD successfully attached. A new drive letter appears (e.g. F:).
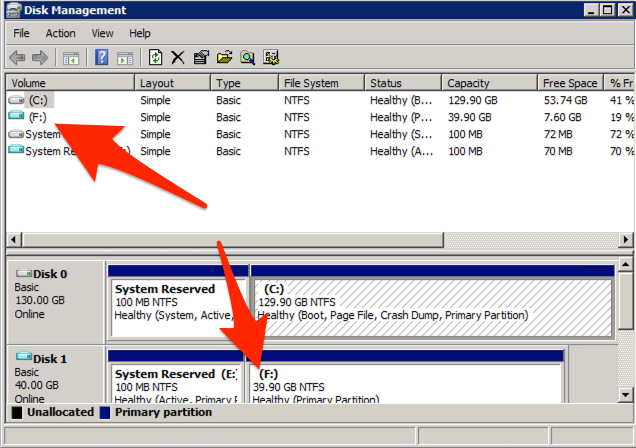
Navigating to the new drive letter will allow you to access the hard drive contents of the domain controller. Specifically, in this case we want to extract the NTDS.dit and the SYSTEM file.
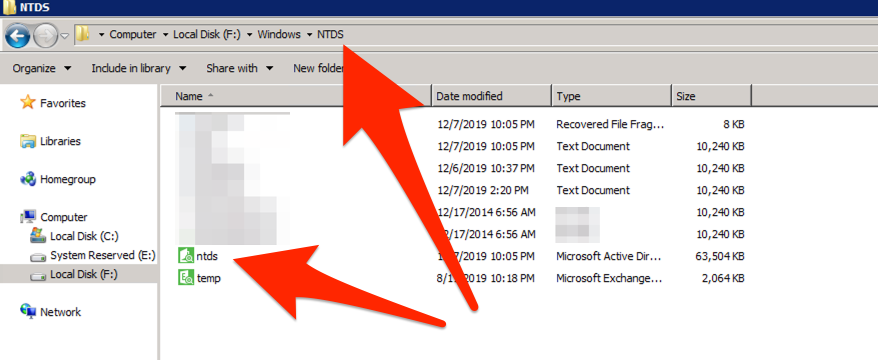
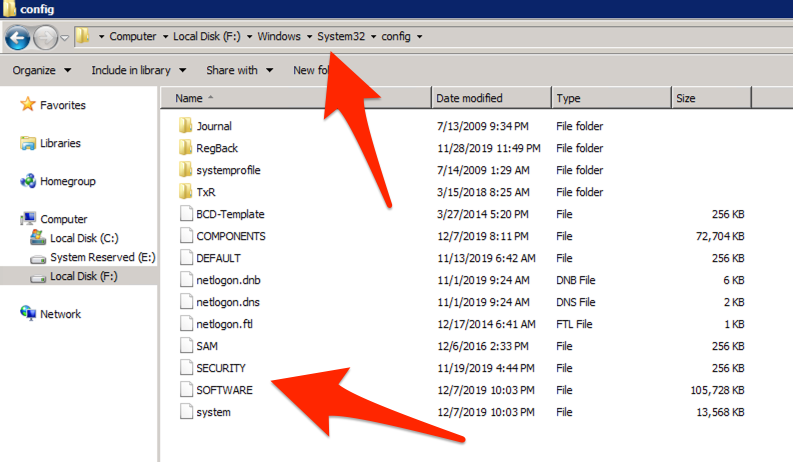
With these files an individual could utilize multiple different tools to extract out the Active Directory domain password hashes for all users. In this engagement I was able to utilize a Domain Administrator’s password hash to validate that I could log into a server on the client’s network.
Remediation:
Looking deeper into VEEAM’s backup configuration manual – the backup process can encrypt the backups utilizing a password. This alone would have prevented me from extracting these server backups. If your organization utilizes any backup software – ensure that it is encrypting the backups as well as they are being stored in a secured location.
